-
Type:
Bug
-
Resolution: Duplicate
-
Priority:
Minor - P4
-
None
-
Affects Version/s: 3.6.18
-
Component/s: Packaging
-
None
-
ALL
-
-
Security 2020-06-29, Security 2020-07-13
-
None
-
None
-
None
-
None
-
None
-
None
-
None
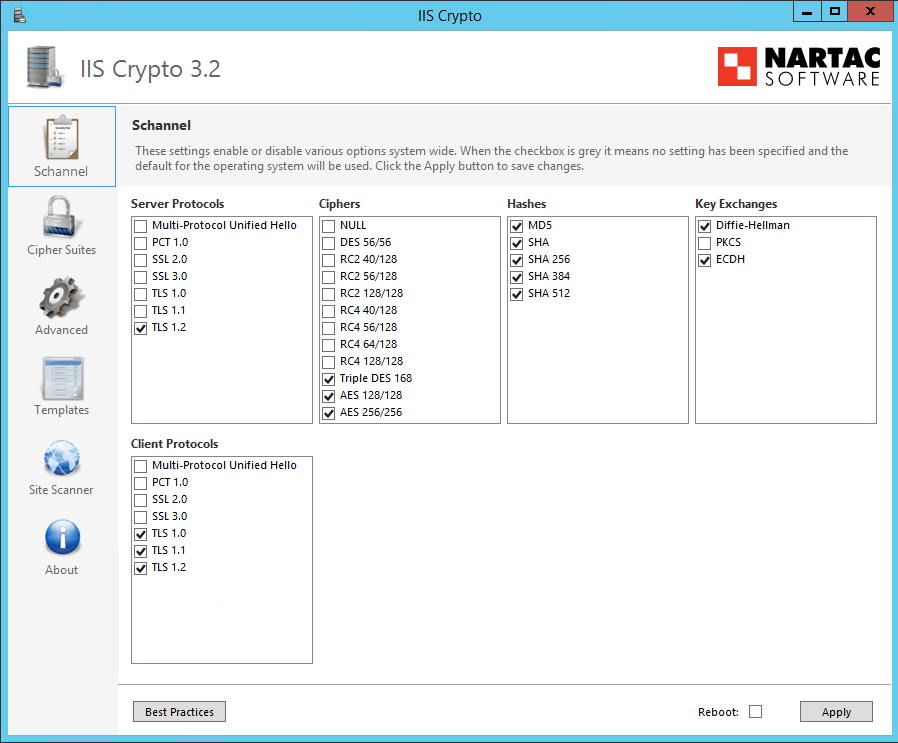
C# client libraries running on Windows 2012 R2 with select SChannel algorithms disabled as below seen from IISCrypto:
Connecting with TLS 1.2 with client certificate presented to CentoOS 7 mongod, rpm version:
mongodb-org-server-3.6.18-1.el7.x86_64
Connection fails with the below log lines when full verbosity enabled:
020-05-22T03:12:54.931+0000 I NETWORK [listener] connection accepted from 10.4.3.137:62577 #85 (5 connections now open)
2020-05-22T03:12:54.931+0000 D EXECUTOR [listener] Starting new executor thread in passthrough mode
2020-05-22T03:12:54.932+0000 D NETWORK [conn85] Session from 10.4.3.137:62577 encountered a network error during SourceMessage
2020-05-22T03:12:54.932+0000 I NETWORK [conn85] end connection 10.4.3.137:62577 (4 connections now open)
Shared ciphers reported under these conditions are:
ECDHE-RSA-AES256-SHA384:ECDHE-RSA-AES128-SHA256:ECDHE-RSA-AES256-SHA:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-ECDSA-AES256-SHA:ECDHE-ECDSA-AES128-SHA
Having the C# driver connect to 'openssl s_server' with these ciphers gives a successful connection. Connecting to mongod using 'openssl s_client' with these ciphers set results in the same disconnection the C# driver sees.
Replacing mongod with a locally compiled binary of 3.6 produces a mongod that does accept connections under these conditions.
- duplicates
-
SERVER-36616 Enable ECDHE support if platform supports it
-
- Closed
-
